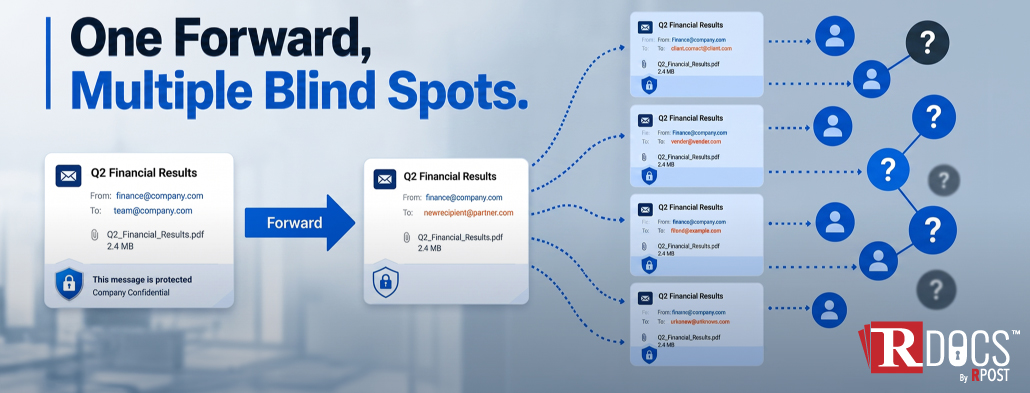
That is increasingly how sensitive information leaves organizations today.
Documents are becoming attack surfaces because the most sensitive business information no longer stays inside one protected environment.
External exposure refers to what happens when a document moves beyond controlled environments and into spaces where visibility and governance no longer exist. This is not a rare edge case. It is the default behavior of how documents move today.
Organizations spend significant budgets on firewalls, endpoint protection, and access controls. Yet year after year, the most consistent source of data breaches isn't a sophisticated exploit — it's a person making a mistake. And when that mistake involves a sensitive document, the consequences can be immediate and severe.
One of the most underappreciated ways customer data slips out of an organization has nothing to do with sophisticated cyberattacks or dramatic breach headlines. It happens through ordinary business documents — contracts, compliance files, proposals, board decks, customer forms — files that move through normal workflows all day long.
May 15, 2026

May 08, 2026

April 30, 2026

April 23, 2026
April 16, 2026