“A sensitive email sent to a mistyped Gmail address is likely to land in some real person’s inbox. Get an email mis-send kill switch with RPost. Just switch it!”
Armand the armadillo here, RPost’s product evangelist. While wandering across the blowing sand dunes outside of Dubai to visit with some of our UAE customers, I got thinking…
In the digital realm, where a single misplaced click can dispatch sensitive information into the abyss of the internet, the concept of "Mis-Sent" has evolved into a significant cybersecurity concern, particularly for legal professionals and their clientele.
At one recent Florida Bar CLE technology webinar, we asked how many lawyers had mis-sent a sensitive document to the wrong party by email. In the poll, 75% of those polled had indicated that they “knew of someone” who had sent a sensitive document to the wrong person.
When we asked the same question among financial services professionals, two thirds said they had made that mistake. The fact remains that some forms of imperfection are not worth having any nostalgia over and can cost careers and untold sums of money.
Remember, there are 1.5 billion Gmail accounts that are active, so even a seemingly innocuous mistyped Gmail address is likely to land in some real person’s inbox.
And, many a lawyer, financial professional, insurance executive, real estate guru, and other businesspeople has been fooled by the misdirected comfort of Microsoft's email “recall” function; while those in the know, know this offers little solace. In short, the Microsoft “recall” feature recalls nothing -- it's widely regarded as ineffective in truly mitigating the damage (unless used within a company or on the same mail server). It does nothing other than send a follow-up email notifying the recipient that the sender would like to have the email recalled. This generally makes the unintended recipient more alert and curious and often causes more inspection of the mis-directed data.
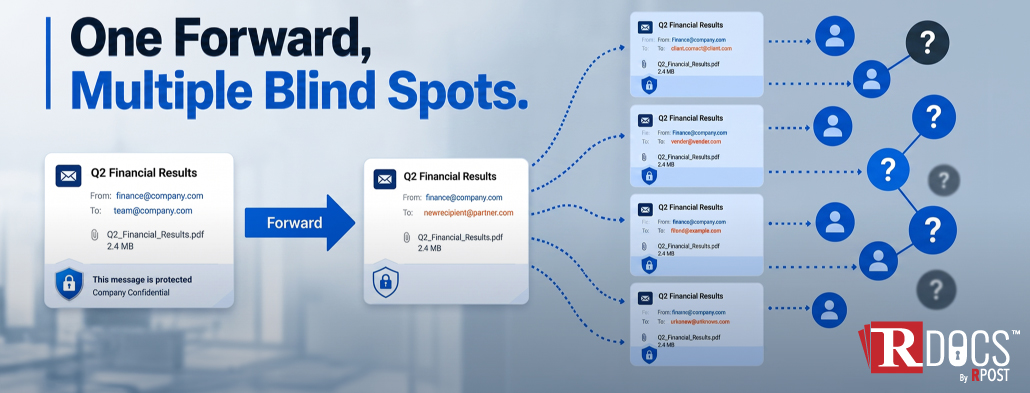
These issues not only compromise sensitive data but also pose the challenging question: was the mis-sent email a reportable breach?
Mis-Sent Emails: A Digital Faux Pas with Real Consequences
The crux of the matter lies in human error—sending an email to the wrong recipient. A seemingly small mistake can lead to substantial repercussions, including the exposure of sensitive information. The moment of realization often comes too late, after the send button has been hastily clicked. The aftermath? A potential data breach notification to your clients; a situation no one wants to find themselves in, compounded by the embarrassment and the risk of sensitive information falling into the wrong hands.
The ideal solution would allow senders to kill a mis-sent file even after sending and delivery, and additionally, see if the unintended recipient accessed the mis-sent email, providing a semblance of control over the situation. Finally, if the misdirected file was not seen, wouldn’t it be great if one could record evidence that the unintended leak did not constitute a reportable breach as the file was remotely killed before being viewed by an unintended human? Of course, it would!
What is happening today? In small law firms, financial, insurance, real estate and in other companies, most try to pretend it didn’t happen. In larger firms with large IT groups, if IT staff are called in a panic with a “what do we do now” request from the person who mis-sent the file, according to some law firm CIOs that we have discussed this with, the IT staff research and try to contact the “wrong” recipient, contact the “wrong” recipient, and ask nicely to see if the “wrong” recipient would delete the email and then send a note to the IT staff saying, “Hey, I deleted the unintended email and did not look at it.” This is generally then considered a non-reportable breach.
However, it is hardly a foolproof plan or optimal record of a leak being a non-breach.
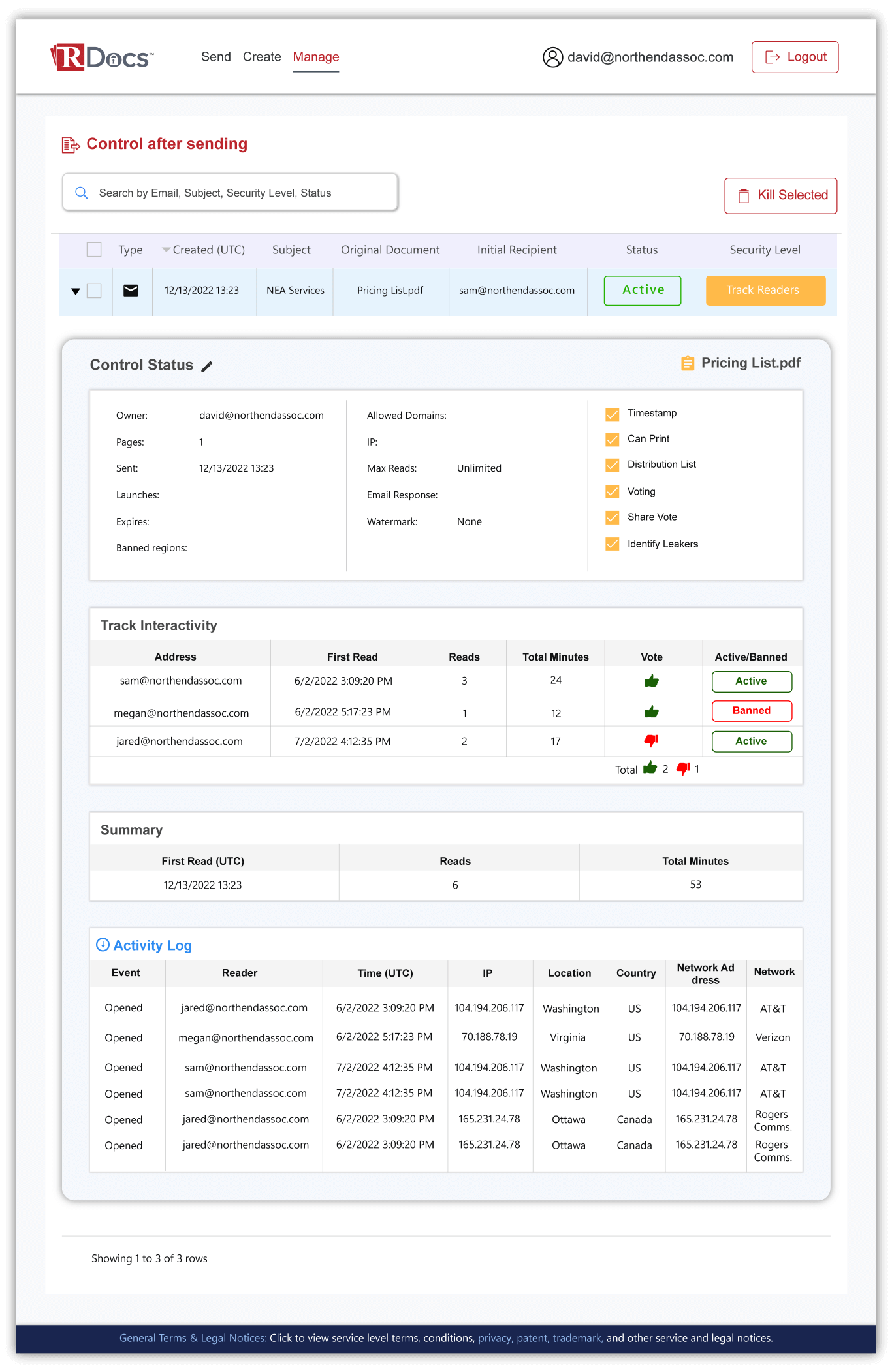
Enter RDocs™ document security: To Send a PDF or an RPD?
A simple solution to this problem is, instead of sending sensitive information in a PDF file format as an attachment, click a button (in RPost tools) to send it as an RPD file format (RPD stands for Rights Protected Document format). For the intended viewer, their viewing experience is the same as viewing a PDF in any browser PDF viewer. For the sender, however, they remain in control of the file even after delivery. They have remote-control-esque power over the file, to see interactivity with it and to kill it after the send, or weeks later after delivery, if desired.
A remote-control-killed file is like burning all the meaty content out of the inside, it just leaves the file carcass, unusable.
Imagine a world where every outbound email, especially those laden with attachments containing sensitive content (think PDFs with litigation strategies, closing documents with wire transfer details, or client invoices with details on matter information, etc.), is safeguarded automatically. With the RDocs™ service, this isn't a mere fantasy. And, it works with one’s existing email service and email flows.
These tools offer the ability to track whether emails and shared documents have been accessed and by whom, providing peace of mind and a tangible layer of security. This technology is not just about damage control; it's a proactive measure to ensure that even if human error occurs, the sender retains a degree of oversight and control over the situation.
Moreover, the sending organization can revoke access to a sensitive document even after it has been delivered, either automatically or manually, and obtain auditable evidence that, despite the document's leakage, access was terminated before the unintended recipient could view it.
Automating Human Error Protections
RPost's technology excels in automating this protective mechanism, ensuring that all outbound emails containing specific types of attachments are covered. This isn't just a feature—it's a necessity in today's fast-paced digital environment, where the difference between security and breach can hinge on a single email.
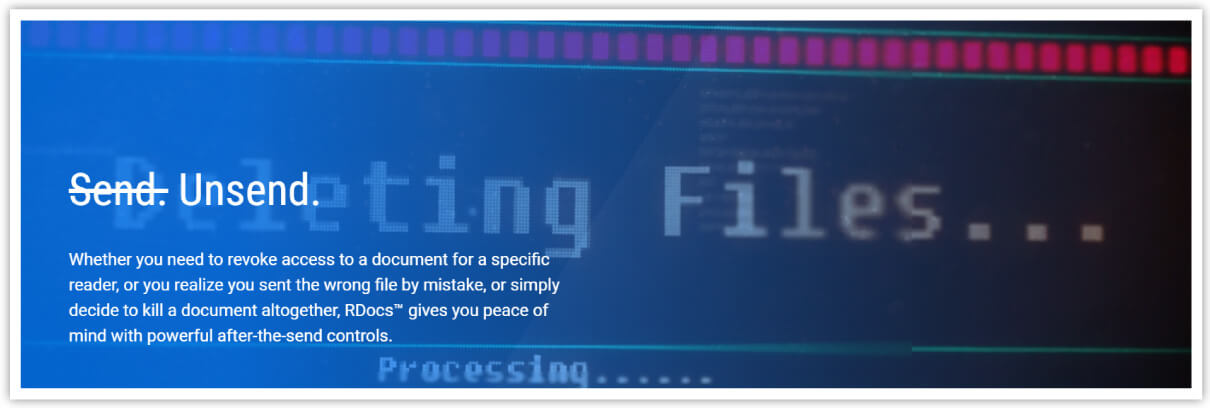
While the digital age brings unparalleled convenience and speed to our communications, it also introduces vulnerabilities that can have serious legal and reputational consequences. RPost stands at the forefront of cybersecurity solutions, providing the tools needed to navigate these challenges confidently. Whether it's a mis-sent email or the threat of cybercriminal activities, RPost offers a beacon of hope, ensuring that your digital communications are secure, controlled, and compliant. After all, in the realm of cybersecurity, it's better to be proactive than reactive.
May 15, 2026

May 08, 2026

April 30, 2026

April 23, 2026
April 16, 2026