
Most organizations believe document security is handled at the point of delivery.
Encrypt the file. Send it. Done.
But that assumption breaks down quickly in real-world workflows.
Because once a document is opened, downloaded, or forwarded, it enters a phase where external exposure becomes the primary risk—and most security controls no longer apply.
External exposure refers to what happens when a document moves beyond controlled environments and into spaces where visibility and governance no longer exist. This is not a rare edge case. It is the default behavior of how documents move today.
The moment a recipient downloads a file, it is no longer bound by the sender’s system. It can be copied, shared, stored, or accessed without restriction. At that point, the document becomes independent of its origin.
This is the exact moment where control is lost—not when the file is intercepted, but when it is successfully delivered.
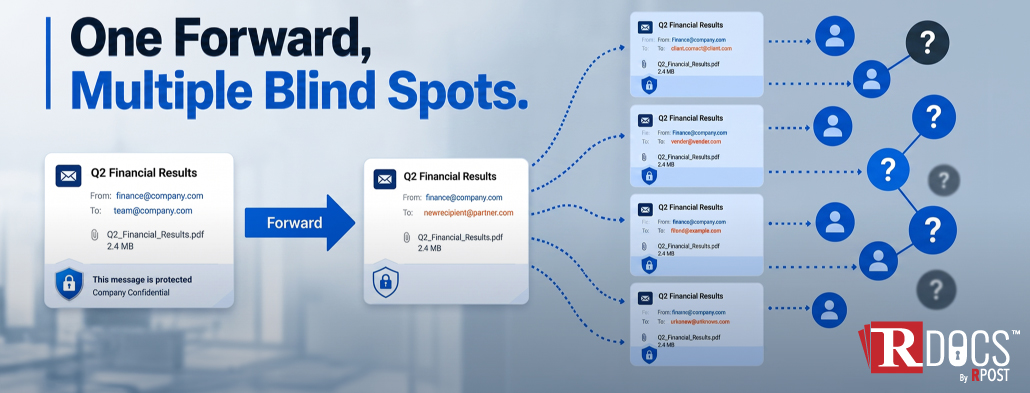
Documents rarely stay where they are first received. They move.
A contract shared with a counterparty may be forwarded internally. A financial statement may be saved on a personal device for later review. A sensitive report may be uploaded into another system for collaboration.
None of these actions are inherently malicious. But they create an environment where control disappears.
This is where Shadow IT plays a role. Teams use tools and channels outside formal governance—personal email, messaging platforms, unmanaged storage—simply because they are convenient. Once a document enters this ecosystem, it becomes invisible to the sender.
There is no reliable way to answer basic questions:
Who accessed it?
Was it shared further?
Is it still being used?
For roles responsible for compliance and risk, that lack of visibility is the problem.
Most document protection strategies are built around two ideas: securing the file during transfer and controlling access at the point of entry.
Both have limitations.
Encryption protects the document while it is in transit. It ensures that the intended recipient is the one who opens it. But once opened, encryption has done its job. The document is now readable, copyable, and distributable.
Portals attempt to extend control by keeping documents inside managed environments. In theory, this preserves access control. In practice, users often download files for ease of use. Once downloaded, the same problem reappears—control is gone.
These models assume that security can be enforced at a single point in time. External exposure proves otherwise.
To address external exposure, the model needs to change.
Documents cannot be treated as static files that are sent and forgotten. They need to be treated as assets that remain under control throughout their lifecycle.
This means the document itself must carry its own controls, rather than relying on the system it was sent through.
The focus shifts from “secure delivery” to persistent control.
Control should not depend on where the file is stored or how it is shared. It should remain active regardless of what happens after the send.
Post-delivery control is not about adding friction for the recipient. It is about ensuring that the sender retains authority over the document, even after it has been accessed.
In practical terms, this includes the ability to revoke access remotely. If a document is sent to the wrong recipient, or if access needs to change, the sender should be able to make that adjustment instantly. The document should no longer be usable, even if it has already been downloaded.
Control also extends to restricting access based on identity and context. A document can be limited to specific users, networks, or locations. If it is forwarded outside those boundaries, it becomes inaccessible. This directly reduces unauthorized document forwarding and limits exposure.
Visibility is equally important. Secure document tracking post-delivery allows organizations to understand how documents are being used. Not in a superficial way, but in terms of actual access patterns—who opened it, when, and under what conditions.
This visibility also supports anomaly detection. If access patterns change—such as unexpected locations or unusual behavior—it can indicate risk. Systems can respond by restricting or locking access before the document is misused.
Finally, there is the issue of leaks. Traditional controls do little to prevent or trace unauthorized sharing. Techniques such as steganographic watermarking embed identifiers within the document itself, making it possible to trace the source of a leak without relying on visible markings.
Together, these capabilities shift the model from passive protection to active control.
In finance, a leaked document can impact transactions or expose sensitive financial data.
In healthcare, it can involve regulated patient information.
In intellectual property law, it can compromise proprietary content or legal strategy.
In each case, the risk is not limited to unauthorized access at the point of delivery. It comes from what happens afterward—when documents move beyond intended boundaries.
External exposure introduces uncertainty into environments that depend on control, traceability, and accountability.
Addressing this challenge requires a different approach—one where documents remain under the sender’s control even after they are shared.
This is the model behind RDocs by RPost.
Instead of sending static files, documents are converted into Rights Protected Documents (RPD™), where security controls are embedded directly into the file itself. This allows the document to remain connected to the sender’s control layer, regardless of where it is stored or how it is accessed.
The result is a shift from “send and lose control” to “send and retain authority.”
Access can be modified, restricted, or removed even after delivery. Visibility continues beyond the first open. And the document behaves as a controlled asset rather than an exposed file.
This aligns with a broader zero-trust approach to information handling—where trust is continuously evaluated, not assumed at a single point in time.
May 29, 2026
May 15, 2026

May 08, 2026

April 30, 2026

April 23, 2026