
Organizations spend significant budgets on firewalls, endpoint protection, and access controls. Yet year after year, the most consistent source of data breaches isn't a sophisticated exploit — it's a person making a mistake. And when that mistake involves a sensitive document, the consequences can be immediate and severe.
According to widely cited research from IBM and the Ponemon Institute, human factors — accidental or manipulated — contribute to the majority of security incidents globally. Documents sit at the center of many of these incidents, because documents carry the information attackers want most: contracts, financial data, personal records, and proprietary communications.
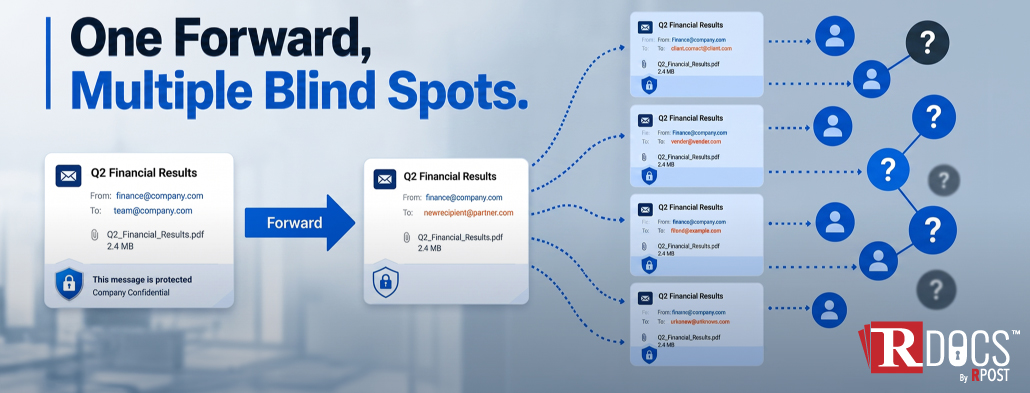
Misdirected email is one of the most underestimated risks in enterprise environments. An employee sends a confidential contract to the wrong address, attaches the wrong file version, or copies an external party on a message never intended for them. These aren't edge cases — they happen at scale, every day, across organizations of every size.
Beyond accidental exposure, phishing attacks specifically exploit human decision-making. A well-crafted phishing email doesn't look suspicious — it looks like a routine document request or an invoice approval. The employee clicks, credentials are compromised, and suddenly the attacker has access to far more than one document.
Weak or reused passwords remain a persistent problem. Even when organizations implement document management platforms or cloud storage, access controls are only as strong as the credentials protecting them. If an employee uses the same password across personal and professional accounts and that password is exposed in an unrelated breach, document access follows shortly after.
Security awareness training is a necessary investment, but it's not a complete solution. Training addresses knowledge gaps — it doesn't account for fatigue, time pressure, or the way modern work is structured. An employee who correctly identifies a phishing attempt 99 times may still click on the hundredth when they're distracted, rushed, or operating under a deadline.
Remote and hybrid work environments compound this further. Documents move across personal devices, home networks, and collaboration platforms that weren't designed with enterprise security standards in mind. The attack surface for human error has expanded significantly, even as training programs have stayed relatively static.
There's also the insider threat dimension. Not all document leaks are accidental. Some involve employees — current or departing — who intentionally extract sensitive information. The challenge is that legitimate document access and malicious extraction can look identical from a systems perspective unless monitoring and controls are specifically designed to detect behavioral anomalies.
The organizations that manage human error most effectively don't rely on behavior change alone. They implement controls that reduce the consequence of a mistake even when the mistake takes place.
For document security, this means combining encrypted delivery, recipient verification, and audit trails into standard document workflows. When a document is sent through a system that logs delivery, confirms the recipient's identity, and restricts unauthorized forwarding or download, a misdirected email becomes a recoverable incident rather than a reportable breach.
RDocs® addresses these failure modes at the infrastructure level. Controlled document access ensures that only verified recipients can open, view, or act on a file — regardless of where it ends up. Confirmed delivery creates an auditable record that proves not just that a document was sent, but that it was received by the right party. Together, these controls transform misdirected emails and unauthorized sharing from reportable breaches into recoverable, documented events. This approach aligns with compliance frameworks like HIPAA, GDPR, and SOC 2.
May 29, 2026
May 15, 2026

May 08, 2026

April 30, 2026

April 23, 2026