
Documents are becoming attack surfaces because the most sensitive business information no longer stays inside one protected environment. Contracts move from legal teams to clients. Financial reports move between advisors, auditors, and investors. M&A documents move across bankers, law firms, board members, and outside consultants.
Security teams have spent years defending networks, endpoints, inboxes, and cloud platforms. That work still matters. But in many high-stakes workflows, the real target is not the system. It is the document.
Attackers do not always need to break into a network if the information they want is already moving through email threads, third-party portals, shared folders, personal devices, and external collaboration channels. They can wait for the file to travel. Once it leaves the sender’s environment, the question becomes simple: who controls it now?
An attack surface is any place where sensitive information, systems, or processes can be accessed, abused, or exposed. Traditionally, this meant servers, endpoints, applications, cloud accounts, and user credentials.
But modern business does not operate inside clean boundaries. Sensitive files are constantly shared with people outside the organization. A law firm shares privileged documents with co-counsel. A private equity team shares diligence files with external advisors. A finance team shares forecasts with auditors or lenders. A board packet moves between executives, assistants, and directors.
Each share creates a new point of exposure.
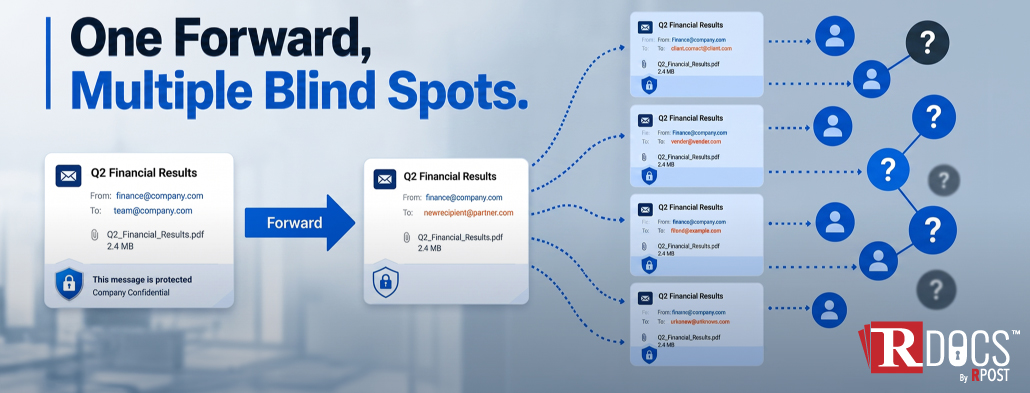
The risk is not only that someone hacks a system. The risk is that the document lands somewhere the original sender can no longer govern. It may be downloaded. Forwarded. Stored in a personal folder. Opened from an unmanaged device. Shared with someone who was never meant to see it.
That is why documents are becoming attack surfaces. They carry the value attackers want, and they often travel beyond the security controls designed to protect them.
A sensitive document becomes an attack surface when it contains valuable information and can be accessed, copied, forwarded, or misused outside the sender’s control.
This is especially true for documents containing:
The document is not passive. It can create risk long after it is sent.
A financial model sent to the wrong party can affect negotiations. A legal memo forwarded outside privilege boundaries can create serious exposure. A draft acquisition document viewed by an unintended recipient can trigger reputational, regulatory, or competitive damage.
The issue is not simply file sharing. The issue is loss of control after sharing.
In law, finance, and M&A, the value of information is often tied to timing. A document does not need to be leaked publicly to cause harm. It only needs to be seen by the wrong person at the wrong moment.
In these workflows, “who has access?” is not enough. Leaders also need to know who viewed the content, when they viewed it, where they viewed it from, and whether access can be revoked if risk appears.
Network security, endpoint protection, secure email gateways, and cloud access controls are necessary. But they are not designed to solve every post-delivery document risk.
They can help protect systems. They can help scan attachments. They can enforce access inside managed platforms. But once a document is delivered, downloaded, forwarded, or opened in a third-party environment, control often becomes fragmented.
This is where many security models fail. They protect the route but not the object.
A secure portal may protect access while the file stays inside the portal. Encryption may protect content during delivery. A password may restrict first access. But none of these automatically guarantee persistent control over the document after it reaches the recipient.
That is the gap document-centric security is meant to address.
Document-centric security starts with a simple idea: security should stay with the document itself, even after it has been sent, downloaded, forwarded, or opened outside the company’s systems. Instead of protecting only the network or the email used to send the file, this approach keeps control attached to the document wherever it goes.
Instead of treating the document as a static file, this model treats it as a controlled asset. The sender should be able to manage access, monitor engagement, restrict use, and revoke availability even after the document leaves the original environment.
This matters because modern data exfiltration prevention is not only about stopping large database theft or malware-driven extraction. It is also about preventing sensitive business content from leaking through routine workflows.
In many cases, exposure happens through ordinary business activity: sending, forwarding, downloading, sharing, reviewing, and re-sharing. That is exactly why post-delivery control matters.
A strong secure document sharing platform should help answer practical questions:
Who opened the document?
Where was it opened from?
How many times was it accessed?
Can access be restricted by recipient or location?
Can the sender revoke access after delivery?
Can sensitive content be disabled if a mistake or threat is detected?
These controls matter because access decisions change. A recipient may be appropriate today but not next week. A deal may end. A vendor relationship may change. A message may be sent to the wrong person. A recipient account may become compromised.
Static permissions are not enough when risk changes after the file is sent.
RDocs® approaches this problem from the view that senders need control beyond delivery. Its patented RPD™ technology is designed to give organizations persistent control over sensitive documents after they are shared.
Instead of relying only on the network, inbox, or storage platform, RDocs® supports a document-centric security model with capabilities to track, restrict, and kill access after sending.
That means organizations can manage document access more actively. They can control who views sensitive content, restrict viewing conditions, monitor engagement, and disable access when a document should no longer be available.
For executives, legal leaders, and deal teams, this changes the security conversation. The question is no longer only, “Did we send it securely?” The better question is, “Can we still control it after it has been sent?”
That is the shift from perimeter-based thinking to post-delivery control.
May 29, 2026
May 15, 2026

May 08, 2026

April 30, 2026

April 23, 2026